What is VPN?
A VPN encrypts and shields your online activities, ensuring privacy. It breaks digital borders, unlocking geo-restricted content for a liberated online experience. A sentinel for data security and privacy, a VPN opens doors to the vast potential of the internet.
What Does a VPN Server Do For You?
Helps You Unlock Content
VPN servers serve as the keymasters, unlocking access to geo-restricted content. By connecting to servers in different regions, users can seamlessly bypass digital borders, accessing a plethora of global content.
Freedom in a Borderless Internet
In the VPN realm, digital borders dissolve, fostering a borderless internet experience. Streaming services, websites, and applications that were once restricted become accessible, offering users unparalleled freedom in their digital pursuits.
Concealing Your Digital Footprint
The VPN server, akin to a digital cloak, conceals your location by masking your IP address. This cryptographic feat renders you invisible to digital trackers and surveillance, ensuring your online movements remain discreet.
Preventing Data Leaks
AceVPN redefines your online experience with lightning-fast speeds. Our advanced VPN technology ensures seamless connections for streaming, gaming, and business activities. Say goodbye to buffering and lag – AceVPN prioritizes speed without compromising security.
Encryption as the Shield
Through robust encryption, the VPN server erects an impenetrable shield against data breaches on public WiFi. This cryptographic layer becomes the armor, protecting your sensitive information from falling into the wrong hands.
Guardian of Public WiFi
Public WiFi, often a breeding ground for digital threats, transforms into a secure haven in the presence of a VPN server. By intercepting your data before it traverses public networks, the server ensures your information remains shielded from potential cyber adversaries.
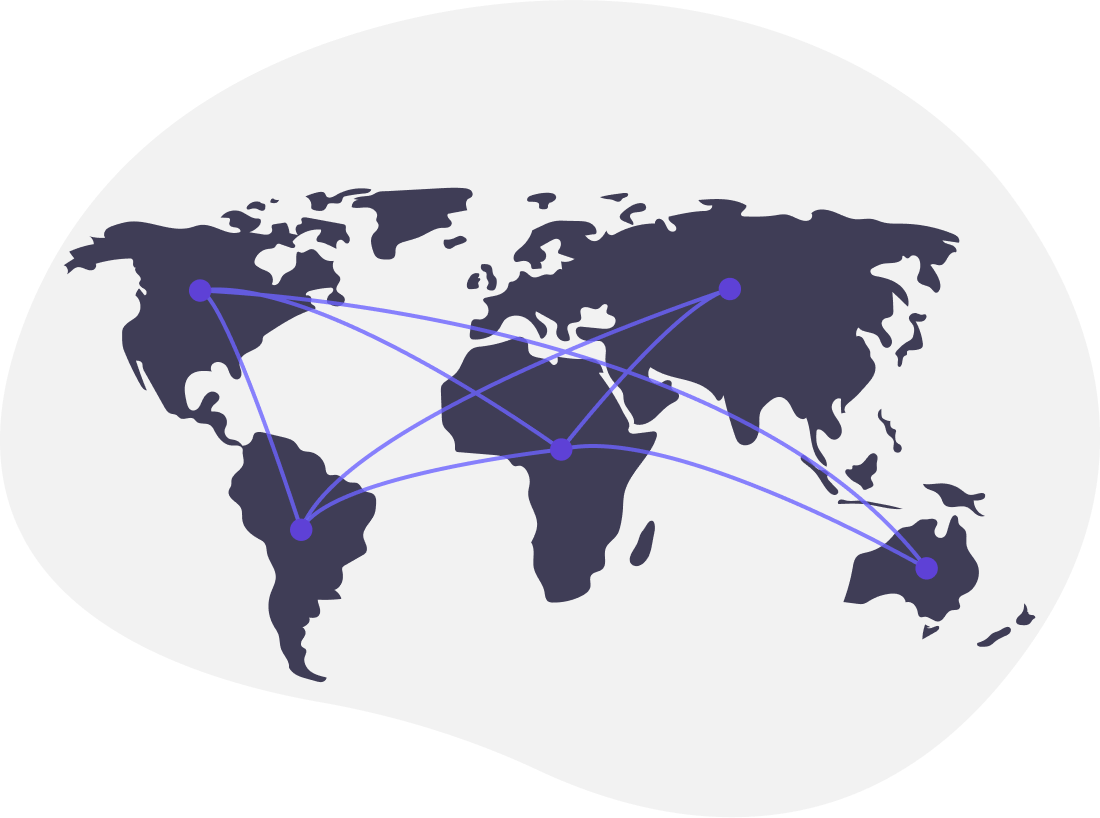
How a VPN Works?
1. Secure Tunnel Initiation
The VPN journey commences with the initiation of a secure tunnel, an impregnable passage that shields your data from prying eyes. This digital tunnel becomes the encrypted pathway for your online activities.

2. Cryptographic Transformation
As your data traverses this secure tunnel, it undergoes a metamorphosis into a cryptographic code. This transformation ensures that your online movements remain elusive, impervious to surveillance, and safeguarded against unauthorized access.

3. VPN Server: The Digital Sentinel
The encrypted data then journeys to a VPN server, a digital fortress where the cryptographic code is unraveled. This server acts as a sentinel, ensuring the secure transmission of decrypted data to its intended destination.

4. Digital Invisibility
Through this intricate process, your online activities attain a state of digital invisibility. The encrypted and decrypted data moves through the secure tunnel, shielding your digital footprint from interception and ensuring a private, secure online experience.

Download AceVPN